
SonicWall NSA 2600 Network Security Appliance
Comprehensive Mid Range Next-Generation Firewall

Call a Specialist Today! (02) 9388 1741


More pricing below, click here!
Please Note: All Prices are Inclusive of GST
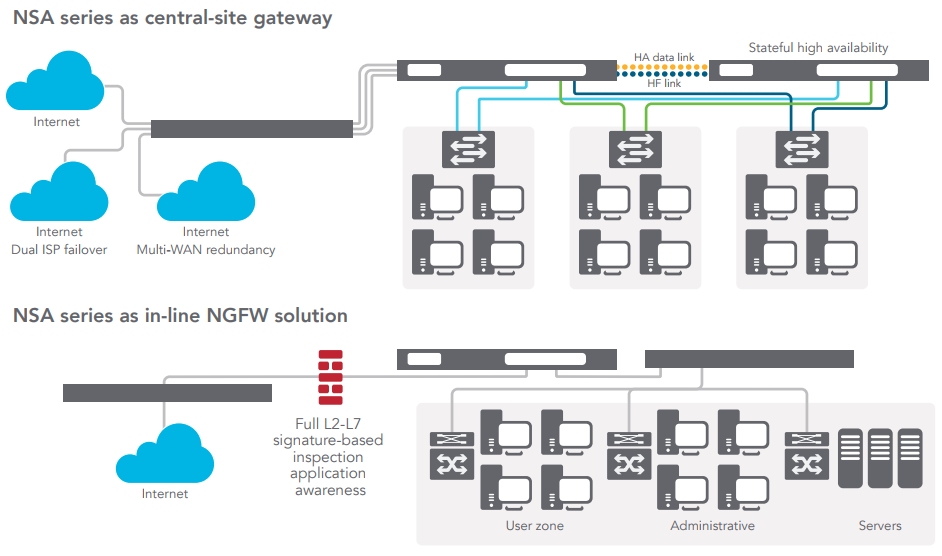
The SonicWall Network Security Appliance (NSA) series provides midsized networks, branch offices and distributed enterprises with advanced threat prevention in a high-performance security platform. Combining nextgeneration firewall technology with our patented* Reassembly-Free Deep Packet Inspection (RFDPI) engine on a multi-core architecture, the NSA series offers the security, performance and control organizations require.
Superior threat prevention and performance
Network control and flexibility
Easy deployment, setup and ongoing management
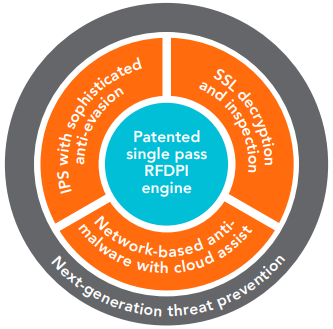
![]() NSA series next-generation firewalls (NGFWs) integrate a series of advanced security technologies to deliver a superior level of threat prevention. Our patented single-pass RFDPI threat prevention engine examines every byte of every packet, inspecting both inbound and outbound traffic simultaneously. The NSA series leverages on-box capabilities including intrusion prevention, anti-malware and web/URL filtering in addition to cloud-based services such as CloudAV and SonicWall Capture multi-engine sandboxing to block zero-day threats at the gateway. Unlike other security products that cannot inspect large files for hidden threats, NSA firewalls scan files of any size across all ports and protocols. The security architecture in SonicWall NGFWs has been validated as one of the industry’s best for security effectiveness by NSS Labs which awarded SonicWall its “Recommended” rating for the fourth consecutive year.
NSA series next-generation firewalls (NGFWs) integrate a series of advanced security technologies to deliver a superior level of threat prevention. Our patented single-pass RFDPI threat prevention engine examines every byte of every packet, inspecting both inbound and outbound traffic simultaneously. The NSA series leverages on-box capabilities including intrusion prevention, anti-malware and web/URL filtering in addition to cloud-based services such as CloudAV and SonicWall Capture multi-engine sandboxing to block zero-day threats at the gateway. Unlike other security products that cannot inspect large files for hidden threats, NSA firewalls scan files of any size across all ports and protocols. The security architecture in SonicWall NGFWs has been validated as one of the industry’s best for security effectiveness by NSS Labs which awarded SonicWall its “Recommended” rating for the fourth consecutive year.
Going beyond intrusion prevention, anti-malware and web filtering, SonicWall NGFWs provide a further level of protection by performing full decryption and inspection of TLS/SSL and SSH encrypted traffic as well as non-proxyable applications, enabling complete protection regardless of transport or protocol. It looks deep inside every packets (the header and data part) searching for protocol non-compliance, threats, zero-days, intrusions, and even defined criteria to detect and prevent hidden attacks that leverage cryptography, block encrypted malware downloads, cease the spread of infections, and thwart command and control (C&C) communications and data exfiltration. Inclusion and exclusion rules allow total control to customize which traffic is subjected to decryption and inspection based on specific organizational compliance and/ or legal requirements.
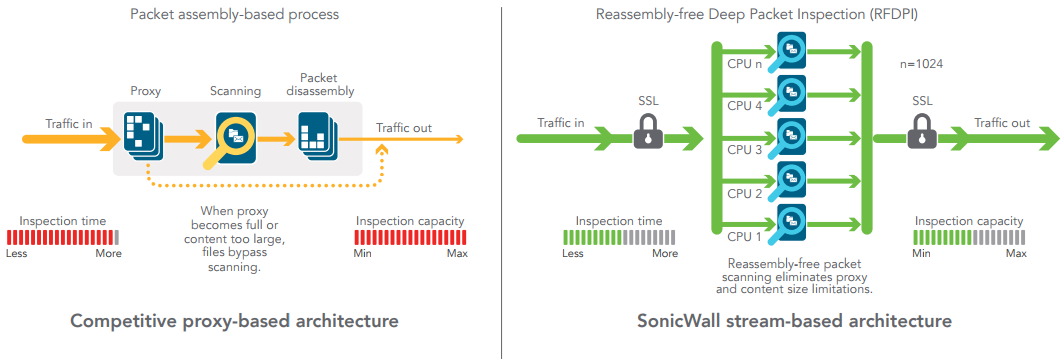
When organizations activate deep packet inspection functions such as intrusion prevention, anti-virus, anti spyware, TLS/SSL decryption/inspection and others on their firewalls network performance often slows down, sometimes dramatically. NSA series firewalls feature a multi-core hardware architecture that utilizes specialized security microprocessors. Combined with our RFDPI engine, this unique design eliminates the performance degradation networks experience with other firewalls.
In today’s security environment, it’s not enough to rely on solely on outside parties for threat information. That’s why SonicWall formed its own in-house threat research team more than 15 years ago. This dedicated team gathers, analyzes and vets data from over one million sensors in its GRID network. SonicWall also participates in industry collaboration efforts and engages with threat research communities to gather and share samples of attacks and vulnerabilities. This shared threat intelligence is used to develop real-time countermeasures that are automatically deployed to our customers’ firewalls.
At the core of the NSA series is SonicOS, SonicWall’s feature-rich operating system. SonicOS provides organizations with the network control and flexibility they require through application intelligence and control, real-time visualization, an intrusion prevention system (IPS) featuring sophisticated antievasion technology, high-speed virtual private networking (VPN) and other robust security features.
Using application intelligence and control, network administrators can identify and categorize productive applications from those that are unproductive or potentially dangerous, and control that traffic through powerful application-level policies on both a peruser and a per-group basis (along with schedules and exception lists). Businesscritical applications can be prioritized and allocated more bandwidth while non-essential applications are bandwidth-limited. Real-time monitoring and visualization provides a graphical representation of applications, users and bandwidth usage for granular insight into traffic across the network.
For organizations that require advanced flexibility in their network design, SonicOS offers the tools to securely segment the network through the use of virtual LANs (VLANs) which enable network administrators to create a virtual LAN interface that allows for network separation into one or more logical groups. Administrators create rules that determine the level of communication with devices on other VLANs.
Built into every NSA series firewall is a wireless access controller that enables organizations to extend the network perimeter securely through the use of wireless technology. Together, SonicWall firewalls and SonicPoint 802.11ac wireless access points create a wireless network security solution that combines industry-leading next-generation firewall technology with high-speed wireless for enterprise-class network security and performance across the wireless network.
Like all SonicWall firewalls, the NSA series tightly integrates key security, connectivity and flexibility technologies into a single, comprehensive solution. This includes SonicPoint wireless access points and the SonicWall WAN Acceleration Appliance (WXA) series, both of which are automatically detected and provisioned by the managing NSA firewall. Consolidating multiple capabilities eliminates the need to purchase and install point products that don’t always work well together. This reduces the effort it takes to deploy the solution into the network and configure it, saving both time and money.
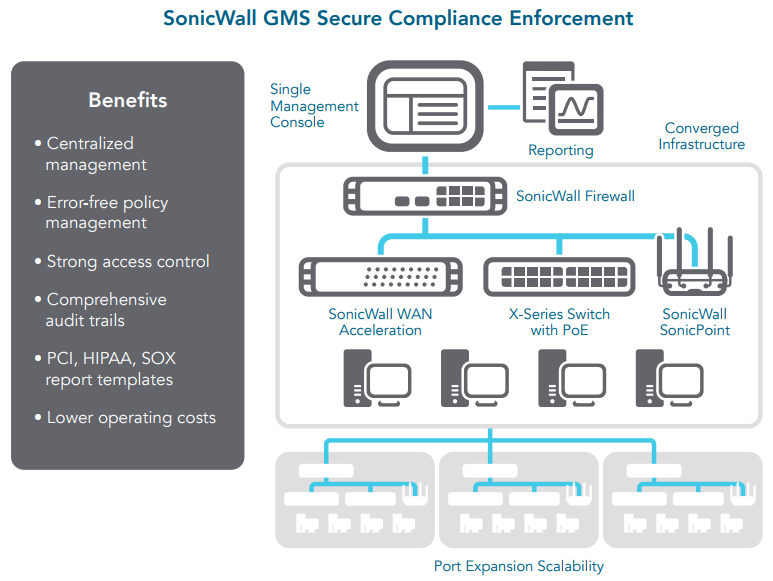
Ongoing management and monitoring of network security are handled centrally through the firewall or through the SonicWall Global Management System (GMS), providing network administrators with a single pane of glass from which to manage all aspects of the network. Together, the simplified deployment and setup along with the ease of management enable organizations to lower their total cost of ownership and realize a high return on investment.
The SonicWall NSA Series next-generation firewalls (NGFWs) utilize the latest multi-core hardware design and Reassembly-Free Deep Packet Inspection to protect the network from internal and external attacks without compromising performance. The NSA Series combines intrusion prevention, content and URL inspection, application intelligence and control, high availability and other advanced networking features.
*U.S. Patents 7,310,815; 7,600,257; 7,738,380; 7,835,361; 7,991,723
| RFDPI Engine | |
|---|---|
| Feature: | Description: |
| Reassembly-Free Deep Packet Inspection (RFDPI) | This high-performance, proprietary and patented inspection engine performs stream-based bi-directional traffic analysis, without proxying or buffering, to uncover intrusion attempts, malware and identify application traffic regardless of port. |
| Bi-directional inspection | Scans for threats in both inbound and outbound traffic simultaneously to ensure that the network is not used to distribute malware, and does not become a launch platform for attacks in case an infected machine is brought inside. |
| Stream-based inspection | Proxy-less and non-buffering inspection technology provides ultra-low latency performance for DPI of millions of simultaneous network streams without introducing file and stream size limitations, and can be applied on common protocols as well as raw TCP streams. |
| Highly parallel and scalable | The unique design of the RFDPI engine works with the multi-core architecture to provide high DPI throughput and extremely high new session establishment rates to deal with traffic spikes in demanding networks. |
| Single-pass inspection | A single-pass DPI architecture simultaneously scans for malware, intrusions and for application identification, drastically reducing DPI latency and ensuring that all threat information is correlated in a single architecture. |
| Firewall and Networking | |
| Feature: | Description: |
| Threat API | All the firewall to receive and leverage any and all proprietary, original equipment manufacturer and third-party intelligence feeds to combat advanced threats such as zero-day, malicious insider, compromised credentials, ransomware and advanced persistent threats. |
| Stateful Packet Inspection | All network traffic is inspected, analyzed and brought into compliance with firewall access policies. |
| High availability/clustering | The NSA Series supports Active/Passive with state synchronization, Active/Active DPI and Active/ Active Clustering high availability modes. Active/Active DPI offloads the Deep Packet Inspection load to cores on the passive appliance to boost throughput. |
| DDoS/DoS attack protection | SYN Flood protection provides a defense against DOS attacks using both Layer 3 SYN proxy and Layer 2 SYN blacklisting technologies. Additionally, it provides the ability to protect against DOS/DDoS through UDP/ICMP flood protection and connection rate limiting. |
| IPv6 support | Internet Protocol version 6 (IPv6) is in its early stages to replace IPv4. With the latest SonicOS 6.2, the hardware will support filtering and wire mode implementations. |
| Flexible deployment options | The NSA Series can be deployed in traditional NAT, Layer 2 Bridge, Wire Mode, and Network Tap modes. |
| WAN load balancing | Load-balances multiple WAN interfaces using Round Robin, Spillover or Percentage methods. Policy-based routing Creates routes based on protocol to direct traffic to a preferred WAN connection with the ability to fail back to a secondary WAN in the event of an outage. |
| Advanced QoS | Guarantees critical communications with 802.1p and DSCP tagging, and remapping of VoIP traffic on the network. |
| H.323 gatekeeper and SIP proxy support | Blocks spam calls by requiring that all incoming calls are authorised and authenticated by H.323 gatekeeper or SIP proxy. |
| Integrated Dell X-Series network switch management | Manage security settings of additional ports, including Portshield, HA, POE and POE+, under a single pane of glass using the SuperMassive management dashboard for Dell’s X series network switch. |
| Biometric Authentication | Supports mobile device authentication such as fingerprint recognition that cannot be easily duplicated or shared to securely authenticate the user identity for network access. |
| Open Authentication and Social Login | Enable guest users to use their credentials from social networking services such as Facebook, Twitter, or Google+ to sign in and access the Internet and other guest services through a host's wireless, LAN or DMZ zones using pass-through authentication. |
| Management and Reporting | |
| Feature: | Description: |
| Global Management System | SonicWall GMS monitors, configures and reports on multiple SonicWall appliances through a single management console with an intuitive interface, reducing management costs and complexity. |
| Powerful single device management | An intuitive web-based interface allows quick and convenient configuration, in addition to a comprehensive CLI and support for SNMPv2/3. |
| IPFIX/NetFlow application flow reporting | Exports application traffic analytics and usage data through IPFIX or NetFlow protocols for realtime and historical monitoring and reporting with tools, such as SonicWall Scrutinizer or other tools that support IPFIX and NetFlow with extensions. |
| Virtual Private Networking | |
| Feature: | Description: |
| Auto-provision VPN | Simplifies and reduces complex distributed firewall deployment down to a trivial effort by automating the initial siteto-site VPN gateway provisioning between SonicWall firewalls while security and connectivity occurs instantly and automatically. |
| IPSec VPN for site-to-site connectivity | High-performance IPSec VPN allows the NSA Series to act as a VPN concentrator for thousands of other large sites, branch offices or home offices. |
| SSL VPN or IPSec client remote access | Utilizes clientless SSL VPN technology or an easy-to-manage IPSec client for easy access to email, files, computers, intranet sites and applications from a variety of platforms. |
| Redundant VPN gateway | When using multiple WANs, a primary and secondary VPN can be configured to allow seamless, automatic failover and failback of all VPN sessions. |
| Route-based VPN | The ability to perform dynamic routing over VPN links ensures continuous uptime in the event of a temporary VPN tunnel failure, by seamlessly re-routing traffic between endpoints through alternate routes. |
| Content/Context Awareness | |
| Feature: | Description: |
| User activity tracking | User identification and activity are made available through seamless AD/LDAP/Citrix/Terminal Services SSO integration combined with extensive information obtained through DPI. |
| GeoIP country traffic identification | Identifies and controls network traffic going to or coming from specific countries to either protect against attacks from known or suspected origins of threat activity, or to investigate suspicious traffic originating from the network. Ability to create custom country and Botnet lists to override an incorrect country or Botnet tag associated with an IP address. Eliminates unwanted filtering of IP addresses due to misclassification. |
| Regular Expression DPI filtering | Prevents data leakage by identifying and controlling content crossing the network through regular expression matching. Ability to create custom country and Botnet lists to override an incorrect country or Botnet tag associated with an IP address. |
| Capture Advanced Threat Protection | |
|---|---|
| Feature: | Description: |
| Multi-engine sandboxing | The multi-engine sandbox platform, which includes virtualized sandboxing, full system emulation, and hypervisor level analysis technology, executes suspicious code and analyzes behavior, providing comprehensive visibility to malicious activity. |
| Broad file type and size analysis | Supports analysis of a broad range of file types, including executable programs (PE), DLL, PDFs, MS Office documents, archives, JAR, and APK plus multiple operating systems including Windows, Android, Mac OSX and multi-browser environments. |
| Rapid deployment of signatures | When a file is identified as malicious, a signature is immediately deployed to firewalls with SonicWall Capture subscriptions and Gateway Anti-Virus and IPS signature databases and the URL, IP and domain reputation databases within 48 hours. |
| Block until verdict | To prevent potentially malicious files from entering the network, files sent to the cloud for analysis can be held at the gateway until a verdict is determined. |
| Encrypted Threat Prevention | |
| Feature: | Description: |
| SSL decryption and inspection | Decrypts and inspects SSL traffic on the fly, without proxying, for malware, intrusions and data leakage, and applies application, URL and content control policies in order to protect against threats hidden in SSL encrypted traffic Included with security subscriptions for all models except SOHO. Sold as a separate license on SOHO. |
| SSH inspection | Deep packet inspection of SSH (DPI-SSH) decrypts and inspect data traversing over SSH tunnel to prevent attacks that leverage SSH. |
| Intrusion Prevention | |
| Feature: | Description: |
| Countermeasure-based protection | Tightly integrated intrusion prevention system (IPS) leverages signatures and other countermeasures to scan packet payloads for vulnerabilities and exploits, covering a broad spectrum of attacks and vulnerabilities. |
| Automatic signature updates | The SonicWall Threat Research Team continuously researches and deploys updates to an extensive list of IPS countermeasures that covers more than 50 attack categories. The new updates take immediate effect without any reboot or service interruption required. |
| Intra-zone IPS protection | Bolsters internal security by segmenting the network into multiple security zones with intrusion prevention, preventing threats from propagating across the zone boundaries. |
| Botnet command and control (CnC) detection and blocking | Identifies and blocks command and control traffic originating from bots on the local network to IPs and domains that are identified as propagating malware or are known CnC points. |
| Protocol abuse/anomaly | Identifies and blocks attacks that abuse protocols in an attempt to sneak past the IPS. |
| Zero-day protection | Protects the network against zero-day attacks with constant updates against the latest exploit methods and techniques that cover thousands of individual exploits. |
| Anti-evasion technology | Extensive stream normalization, decoding and other techniques ensure that threats do not enter the network undetected by utilizing evasion techniques in Layers 2-7. |
| Threat Prevention | |
| Feature: | Description: |
| Gateway anti-malware | The SonicWall RFDPI engine scans all inbound, outbound and intra-zone traffic for viruses, Trojans, key loggers and other malware in files of unlimited length and size across all ports and TCP streams. |
| CloudAV malware protection | A continuously updated database of over 17 million threat signatures resides in the SonicWall cloud servers and is referenced to augment the capabilities of the onboard signature database, providing RFDPI with extensive coverage of threats. |
| Around-the-clock security updates | New threat updates are automatically pushed to firewalls in the field with active security services, and take effect immediately without reboots or interruptions. |
| Bi-directional raw TCP inspection | The RFDPI engine is capable of scanning raw TCP streams on any port bi-directionally preventing attacks that they to sneak by outdated security systems that focus on securing a few well-known ports. |
| Extensive protocol support | Identifies common protocols such as HTTP/S, FTP, SMTP, SMBv1/v2 and others, which do not send data in raw TCP, and decodes payloads for malware inspection, even if they do not run on standard, well-known ports. |
| Application Intelligence and Control | |
| Feature: | Description: |
| Application control | Control applications, or individual application features, that are identified by the RFDPI engine against a continuously expanding database of over thousands of application signatures, to increase network security and enhance network productivity. |
| Custom application identification | Control custom applications by creating signatures based on specific parameters or patterns unique to an application in its network communications, in order to gain further control over the network. |
| Application bandwidth management | Granularly allocate and regulate available bandwidth for critical applications or application categories while inhibiting nonessential application traffic. |
| Granular control | Control applications, or specific components of an application, based on schedules, user groups, exclusion lists and a range of actions with full SSO user identification through LDAP/AD/Terminal Services/Citrix integration. |
| Content Filtering | |
| Feature: | Description: |
| Inside/outside content filtering | Enforce acceptable use policies and block access to websites containing information or images that are objectionable or unproductive with Content Filtering Service. |
| Enforced content filtering client | Extend policy enforcement to block internet content for Windows, Mac and Android devices located outside the firewall perimeter. |
| Granular controls | Block content using the predefined categories or any combination of categories. Filtering can be scheduled by time of day, such as during school or business hours, and applied to individual users or groups. |
| Web caching | URL ratings are cached locally on the SonicWall firewall so that the response time for subsequent access to frequently visited sites is only a fraction of a second. |
| Enforced Anti-Virus and Anti-Spyware | |
| Feature: | Description: |
| Multi-layered protection | Utilize the firewall capabilities as the first layer of defense at the perimeter, coupled with endpoint protection to block, viruses entering network through laptops, thumb drives and other unprotected systems. |
| Automated enforcement option | Ensure every computer accessing the network has the most recent version of anti-virus and anti-spyware signatures installed and active, eliminating the costs commonly associated with desktop anti-virus and anti-spyware management. |
| Automated deployment and installation option | Machine-by-machine deployment and installation of anti-virus and anti-spyware clients is automatic across the network, minimizing administrative overhead. |
| Always on, automatic virus protection | Frequent anti-virus and anti-spyware updates are delivered transparently to all desktops and file servers to improve end user productivity and decrease security management. |
| Spyware protection | Powerful spyware protection scans and blocks the installation of a comprehensive array of spyware programs on desktops and laptops before they transmit confidential data, providing greater desktop security and performance. |
Firewall
SSL/SSH decryption and inspection1
Capture advanced threat protection1
Intrusion prevention1
Anti-malware1
Application identification1
Web content filtering1
VPN
VoIP
Wireless
Networking
Management and monitoring
1 Requires added subscription.
 Achieve deeper network security
Achieve deeper network securitySonicWall NSA Series firewalls are capable of providing organizations of any size with a deeper level of network security because they are designed using a scalable, multi-core hardware architecture and a patented, single-pass, low-latency, Reassembly-Free Deep Packet Inspection (RFDPI) engine that can scan every byte of every packet while maintaining high performance. The SonicWall NSA Series goes deeper than other firewalls with an RFDPI engine that combines real-time SSL decryption and inspection, an intrusion prevention system (IPS) that features sophisticated anti-evasion technology and a network-based malware protection system that leverages the power of the cloud. Now organizations can block daily new threats as they appear.
It is estimated that organizations are blind to approximately one third of their network traffic due to SSL encryption. SSL Decryption and Inspection technology available on the SonicWall NSA Series enables the RFDPI engine to decrypt and inspect all of network traffic on every port.
Every hour new variants of malware are developed. The SonicWall NSA Series keeps you abreast of these threats with network-based malware protection that leverages a cloud database which is updated continually and currently contains more than 13 million variants of malware.
The SonicWall Intrusion Prevention Service (IPS) protects against an array of network-based application vulnerabilities and exploits. New application vulnerabilities are discovered every day making ongoing IPS updates critical in keeping protection up to date from emerging threats. SonicWall goes a step beyond traditional solutions with an intrusion prevention system that features sophisticated anti-evasion technology. It scans all network traffic for worms, Trojans, software vulnerabilities, backdoor exploits, and other types of malicious attacks. Cybercriminals often try to circumvent the IPS by using complex algorithms to evade detection. SonicWall NGFWs feature advanced threat protection to decode hidden attacks before they can harm your organization. By focusing on known malicious traffic, SonicWall IPS filters out false positives while increasing network reliability and performance. Designed to protect against both internal and external threats, SonicWall IPS monitors network traffic for malicious or anomalous behavior, then blocks or logs traffic based on predefined policy.
The SonicWall Reassembly-Free Deep Packet Inspection (RFDPI) engine provides superior threat protection and application control without compromising performance. It relies on streaming traffic payload inspection to detect threats at Layers 3-7, and takes network streams through extensive and repeated normalization and decryption in order to neutralize advanced evasion techniques that seek to confuse detection engines and sneak malicious code into the network.
Once a packet undergoes the necessary pre-processing, including SSL decryption, it is analyzed against a single, proprietary memory representation of three signature databases: intrusion attacks, malware and applications. The connection state is then advanced to represent the position of the stream relative to these databases until it encounters a state of attack, or other "match" event, at which point a pre-set action is taken.
In most cases, the connection is terminated and proper logging and notification events are created. However, the engine can also be configured for inspection only or, in case of application detection, to provide Layer 7 bandwidth management services for the remainder of the application stream as soon as the application is identified.
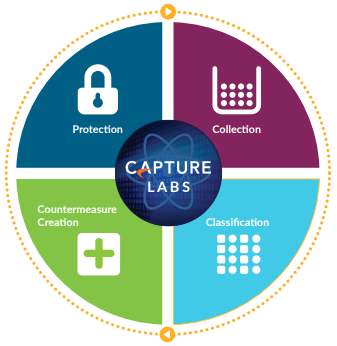
The dedicated, in-house SonicWall Capture Labs threat research team researches and develops countermeasures to deploy to customer firewalls for up-to-date protection. The team gathers data on potential threats from several sources including our awardwinning network sandboxing service, Capture Advanced Threat Protection, as well as more than 1 million SonicWall sensors located around the globe that monitor traffic for emerging threats. It is analyzed via machine learning using SonicWall's Deep Learning Algorithms to extract the DNA from the code to see if it is related to any known forms of malicious code.
SonicWall NGFW customers benefit from continuously updated threat protection around the clock. New updates take effect immediately without reboots or interruptions. The signatures resident on the appliances are designed to protect against wide classes of attacks, covering tens of thousands of individual threats with a single signature.
In addition to the countermeasures on the appliance, NSA appliances also have access to SonicWall CloudAV, which extends the onboard signature intelligence with over 20 million signatures. This CloudAV database is accessed by the firewall via a proprietary, light-weight protocol to augment the inspection done on the appliance. With Capture Advanced Threat Protection, a cloud-based multi-engine sandbox, organizations can examine suspicious files and code in an isolated environment to stop advanced threats such as zeroday attacks.
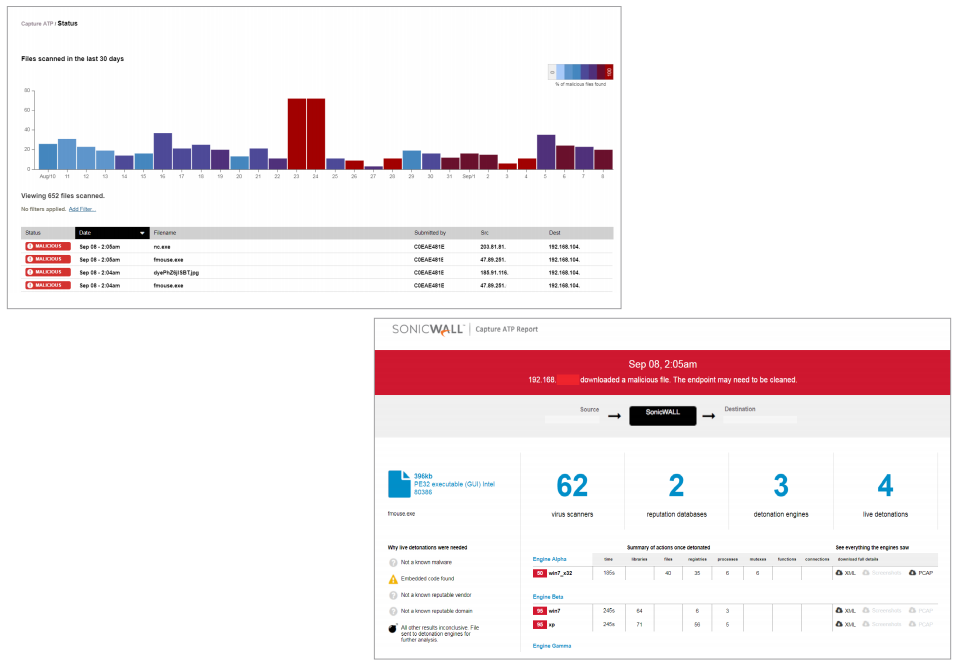
SonicWall Capture Advanced Threat Protection Service is a cloud-based multi-engine sandbox that extends firewall threat protection to detect and prevent zero-day threats. Suspicious files are sent to the cloud for analysis with the option to hold them at the gateway until a verdict is determined. The multi-engine sandbox platform, which includes virtualized sandboxing, full system emulation and hypervisor level analysis technology, executes suspicious code and analyzes behavior. When a file is identified as malicious, a hash is immediately created within Capture and later a signature is sent to firewalls to prevent follow-on attacks.
The service analyzes a broad range of operating systems and file types, including executable programs, DLL, PDFs, MS Office documents, archives, JAR and APK.
Capture provides an at-a-glance threat analysis dashboard and reports, which detail the analysis results for files sent to the service, including source, destination and a summary plus details of malware action once detonated.
For highly regulated organizations wanting to achieve a fully coordinated security governance, compliance and risk management strategy, the optional SonicWall Global Management System (GMS) provides administrators a unified, secure and extensible platform to manage SonicWall firewalls, wireless access points and switches through a correlated and auditable workstream process. GMS enables enterprises to easily consolidate the management of security appliances, reduce administrative and troubleshooting complexities, and govern all operational aspects of the security infrastructure, including centralized policy management and enforcement; realtime event monitoring; user activities; application identifications; flow analytics and forensics; compliance and audit reporting; and more. GMS also meets the firewall’s change management requirements of enterprises through a workflow automation feature. With GMS workflow automation, all enterprises will gain agility and confidence in deploying the right firewall policies, at the right time and in conformance to compliance regulations. GMS provides a coherent way to manage network security by business processes and service levels, dramatically simplifying lifecycle management of your overall security environments as compared to managing on a device-by-device basis.
Every SonicWall NSA appliance utilizes a breakthrough, multi-core hardware design and RFDPI for internal and external network protection without compromising network performance. The NSA series NGFWs combine high-speed intrusion prevention, file and content inspection, and powerful application intelligence and control with an extensive array of advanced networking and flexible configuration features. The NSA series offers an affordable platform that is easy to deploy and manage in a wide variety of large, branch office and distributed network environments.
| Models: | NSA 2600 | NSA 2650 | NSA 3600 | NSA 4600 | NSA 5600 | NSA 6600 |
|---|---|---|---|---|---|---|
| Firewall | ||||||
| SonicOS Version | SonicOS 6.5 | |||||
| Security Processing Cores | 4 | 4 | 6 | 8 | 10 | 24 |
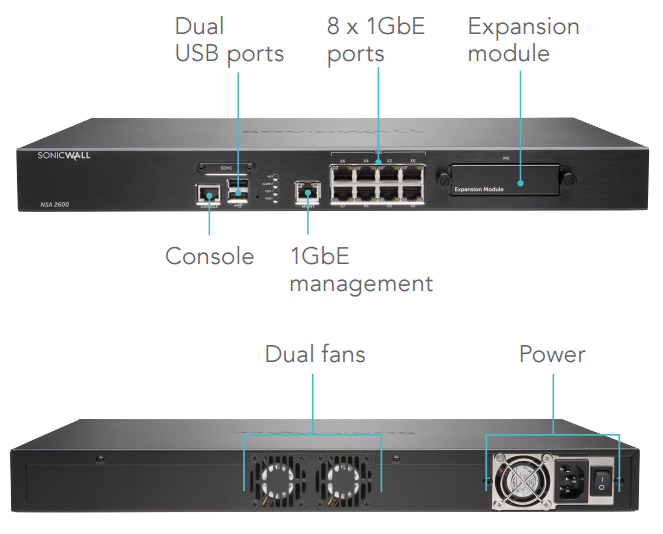
| Interfaces | 8 x 1-GbE, 1 GbE Management, 1 Console |
4 x 2.5-GbE SFP, 4 x 2.5-GbE, 12 x 1-GbE, 1 GbE Management, 1 Console |
2 x 10-GbE SFP+, 4 x 1-GbE SFP, 12 x 1 GbE, 1 GbE Management, 1 Console |
2 x 10-GbE SFP+, 4 x 1-GbE SFP, 12 x 1 GbE, 1 GbE Management, 1 Console |
2 x 10-GbE SFP+, 4 x 1-GbE SFP, 12 x 1 GbE, 1 GbE Management, 1 Console |
4 x 10-GbE SFP+, 8 x 1-GbE SFP, 8 x 1 GbE, 1 GbE Management, 1 Console |
| Management | CLI, SSH, GUI, GMS | |||||
| Expansion | 1 Expansion Slot (Rear)*, SD Card* | 1 Expansion Slot (Rear)*, 16 GB storage module | 1 Expansion Slot (Rear)*, SD Card* | |||
| SSO users | 30,000 | 40,000 | 40,000 | 50,000 | 60,000 | 70,000 |
| Maximum SonicPoints supported | 32 | 48 | 48 | 64 | 96 | 128 |
| Logging | Analyzer, Local Log, Syslog | |||||
| Firewall/VPN Performance | NSA 2600 | NSA 2650 | NSA 3600 | NSA 4600 | NSA 5600 | NSA 6600 |
| Firewall Inspection Throughput1 | 1.9 Gbps | 3.0 Gbps | 3.4 Gbps | 6.0 Gbps | 9.0 Gbps | 12.0 Gbps |
| Full DPI Throughput2 | 300 Mbps | 600 Mbps | 500 Mbps | 800 Mbps | 1.6 Gbps | 3.0 Gbps |
| Application Inspection Throughput2 | 700 Mbps | 1.4 Gbps | 1.1 Gbps | 2.0 Gbps | 3.0 Gbps | 4.5 Gbps |
| IPS Throughput2 | 700 Mbps | 1.4 Gbps | 1.1 Gbps | 2.0 Gbps | 3.0 Gbps | 4.5 Gbps |
| Anti-Malware Inspection Throughput2 | 400 Mbps | 600 Mbps | 600 Mbps | 1.1 Gbps | 1.7 Gbps | 3.0 Gbps |
| IMIX Throughput3 | 600 Mbps | 700 Mbps | 900 Mbps | 1.6 Gbps | 2.4 Gbps | 3.5 Gbps |
| SSL Inspection & Decription (DPI SSL)2 | 200 Mbps | 300 Mbps | 300 Mbps | 500 Mbps | 800 Mbps | 1.3 Gbps |
| VPN Throughput3 | 1.1 Gbps | 1.5 Gbps | 1.5 Gbps | 3.0 Gbps | 4.5 Gbps | 5.0 Gbps |
| Connections per Second | 15,000/sec | 15,000/sec | 20,000/sec | 40,000/sec | 60,000/sec | 90,000/sec |
| Maximum Connections (SPI) | 500,000 | 1,000,000 | 750,000 | 1,000,000 | 1,500,000 | 1,500,000 |
| Maximum Connections (DPI)4 | 250,000 | 500,000 | 375,000 | 500,000 | 1,000,000 | 1,000,000 |
| Maximum Connections (DPI)5 | 1,000/1,000 | 12,000/13,500 | 2,000/2,750 | 3,000/4,500 | 4,000/8,500 | 6,000/10,500 |
| VPN | NSA 2600 | NSA 2650 | NSA 3600 | NSA 4600 | NSA 5600 | NSA 6600 |
| Site-to-Site Tunnels | 250 | 1,000 | 1,000 | 1,500 | 4,000 | 6,000 |
| IPSec VPN clients (Maximum) | 10 (250) | 50 (1,000) | 50 (1,000) | 500 (3,000) | 2,000 (4,000) | 2,000 (6,000) |
| SSL VPN licenses (Maximum) | 2 (250) | 2 (350) | 2 (350) | 2 (500) | 2 (1,000) | 2 (1,500) |
| Encryption/Authentication | DES, 3DES, AES (128, 192, 256-bit)/MD5, SHA-1, Suite B Cryptography | |||||
| Key Exchange | Diffie Hellman Groups 1, 2, 5, 14v | |||||
| Route-Based VPN | RIP, OSPF | |||||
| Networking | NSA 2600 | NSA 2650 | NSA 3600 | NSA 4600 | NSA 5600 | NSA 6600 |
| IP Address Assignment | Static (DHCP PPPoE, L2TP and PPTP client), Internal DHCP server, DHCP Relay | |||||
| NAT Modes | 1:1, many:1, 1:many, flexible NAT (overlapping IPS), PAT, transparent mode | |||||
| VLAN Interfaces | 256 | 256 | 256 | 256 | 400 | 500 |
| Routing Protocols | BGP, OSPF, RIPv1/v2, static routes, policy-based routing, multicast | |||||
| QoS | Bandwidth priority, max bandwidth, guaranteed bandwidth, DSCP marking, 802.1p | |||||
| Authentication | LDAP (multiple domains), XAUTH/RADIUS, SSO, Novell, internal user database, Terminal Services, Citrix, Common Access Card (CAC) | |||||
| VoIP | Full H323-v1-5, SIP | |||||
| Standards | TCP/IP, ICMP, HTTP, HTTPS, IPSec, ISAKMP/IKE, SNMP, DHCP, PPPoE, L2TP, PPTP, RADIUS, IEEE 802.3 | |||||
| Certifications | ICSA Firewall, ICSA Anti-Virus, FIPS 140-2, Common Criteria NDPP (Firewall and IPS), UC APL | |||||
| High availability | Active/Passive with State Sync | Active/Passive with State Sync Active/Active Clustering |
Active/Passive with State Sync, Active/Active DPI with State Sync, Active/Active Clustering |
|||
| Hardware | NSA 2600 | NSA 2650 | NSA 3600 | NSA 4600 | NSA 5600 | NSA 6600 |
| Power Supply | Single, Fixed 200W | Dual, redundant 120W (one included) | Single, Fixed 250W | |||
| Fans | Dual, Fixed | Dual, redundant, hot swappable | ||||
| Input Power | 100-240 VAC, 60-50 Hz | |||||
| Max Power Consumption (W) | 49.4 | 74.3 | 74.3 | 86.7 | 90.9 | 113.1 |
| MTBF @25ºC in hours | 176,540 | 146,789 | 146,789 | 139,783 | 134,900 | 116,477 |
| MTBF @25ºC in years | 20.15 | 16.76 | 16.76 | 15.96 | 15.40 | 13.30 |
| Form Factor | 1U Rack Mountable | |||||
| Dimensions | 1.75 x 19.1 x 17 in (4.5 x 48.5 x 43 cm) |
|||||
| Weight | 10.1 lb (4.6 Kg) | 13.56 lb (6.15 kg) | 13.56 lb (6.15 Kg) | 13.56 lb (6.15 Kg) | 13.56 lb (6.15 Kg) | 14.93 lb (6.77 Kg) |
| WEEE Weight | 11 lb (5.0 Kg) | 14.24 lb (6.46 kg) | 14.24 lb (6.46 Kg) | 14.24 lb (6.46 Kg) | 14.24 lb (6.46 Kg) | 19.78 lb (8.97 Kg) |
| Shipping Weight | 14.3 lb (6.5 Kg) | 20.79 lb (9.43 kg) | 20.79 lb (9.43 Kg) | 20.79 lb (9.43 Kg) | 20.79 lb (9.43 Kg) | 26.12 lb (11.85 Kg) |
| Major Regulatory | FCC Class A, CE (EMC, LVD, RoHS), C-Tick, VCCI Class A, MSIP/KCC Class A, UL, cUL, TUV/GS, CB, Mexico CoC by UL, WEEE , REACH, ANATEL, BSMI, CU | |||||
| Environment | 32°-105° F (0°-40° C)/-40° to 158° F (-40° to 70° C) | |||||
| Humidity | 10-90% non-condensing. | |||||
Notes:
1 Testing Methodologies: Maximum performance based on RFC 2544 (for firewall). Actual performance may vary depending on network conditions and activated services.
2 Full DPI/GatewayAV/Anti- Spyware/IPS throughput measured using industry standard Spirent WebAvalanche HTTP performance test and Ixia test tools. Testing done with multiple flows through multiple port pairs.
3 VPN throughput measured using UDP traffic at 1280 byte packet size adhering to RFC 2544. All specifications, features and availability are subject to change.
4 For every 125,000 DPI connections reduced, the number of available DPI SSL connections increases by 750.
All specifications, features and availability are subject to change.
*Future use.
Leverage SonicWall Advanced Gateway Security Suite (AGSS) to deliver a multi-engine sandbox, powerful anti‐virus, anti‐spyware, intrusion prevention, content filtering, as well as application intelligence and control services. An upgrade over CGSS, this package features Capture Advanced Threat Protection (ATP), a multi-engine sandbox that runs and inspects suspicious files, programs and code in an isolated cloud-based environment.
Get the most from your deep packet inspection firewall with the SonicWall Comprehensive Security Suite (CGSS) subscription. CGSS includes gateway anti-virus, anti-spyware, intrusion prevention, application intelligence and control service, content/URL filtering and 24x7 support. Combine security, productivity and support in a single, bundled solution that lowers TCO.
Enable your business firewall to provide real-time network threat prevention with SonicWall gateway anti-virus, anti-spyware, intrusion prevention and application intelligence and control. Block the latest blended threats - including viruses, spyware, worms, Trojans, software vulnerabilities and other malicious code. Guarantee bandwidth prioritization and ensure maximum network security and productivity with granular policies for both groups and users.
The cloud-based SonicWall Capture Advanced Threat Protection Service scans a broad range of files to detect advanced threats, analyzes them in a multi-engine sandbox, blocks them prior to a security verdict, and rapidly deploys remediation signatures. The result is higher security effectiveness, faster response times and a lower total cost of ownership.
Gain a cost-effective, easy-to-manage way to enforce protection and productivity policies, and block inappropriate, unproductive and dangerous web content in educational, business or government environments. SonicWall Content Filtering Service lets you control access to websites based on rating, IP address, URL and more. You get the ideal combination of control and flexibility to ensure the highest levels of protection and productivity, which you can configure and control from your network security appliance, eliminating the need for a costly, dedicated filtering solution. Extend enforcement of your internal policies to devices located outside the firewall perimeter by blocking unwanted internet content with the content filtering client.
Extend the enforcement of web policies in IT-issued devices outside the network perimeter. Although it doesn't require a firewall, it can be optionally coupled with SonicWall Content Filtering Service as an ideal combination to keep students and employees off of dangerous or non-productive websites by switching to cloud-enforced policies even when they are using roaming devices.
Benefit from advanced technical assistance and ongoing software and firmware updates with SonicWall Dynamic Support. The service includes:
Enjoy the convenience and affordability of deploying your firewall as a SonicWall TotalSecure solution. This combines the hardware and services needed for comprehensive network protection from viruses, spyware, worms, Trojans, key loggers and more - without the complexity of building your own security package.
Block threats from your email server and stop spam at the gateway by adding SonicWall Comprehensive Anti-Spam Service (CASS) to your SonicWall firewall. Rapidly deploy your spam firewall software with one-click activation of up to 250 users.
Execute an innovative, multi-layered, anti-virus internet security strategy with SonicWall firewalls and Enforced Client Anti-Virus and Anti-Spyware software. You get SonicWall Reassembly-Free Deep Packet Inspection anti-malware at the gateway, and enforced anti-virus protection at the endpoints. You can redirect any user with a non-compliant endpoint to a web page to install the latest Enforced Client Anti-Virus and Anti-Spyware software. Provide automatically updated security definitions to the endpoint as soon as they become available. Plus, you can automate enforcement to minimize administrative overhead.
Download the SonicWall NSA Series Datasheet (.PDF)
Pricing Notes: